High-value Stock Handling Checklist
Download your high-value stock checklist
Please fill out the form below to access your free high-value stock checklist download.
About this high-value stock checklist
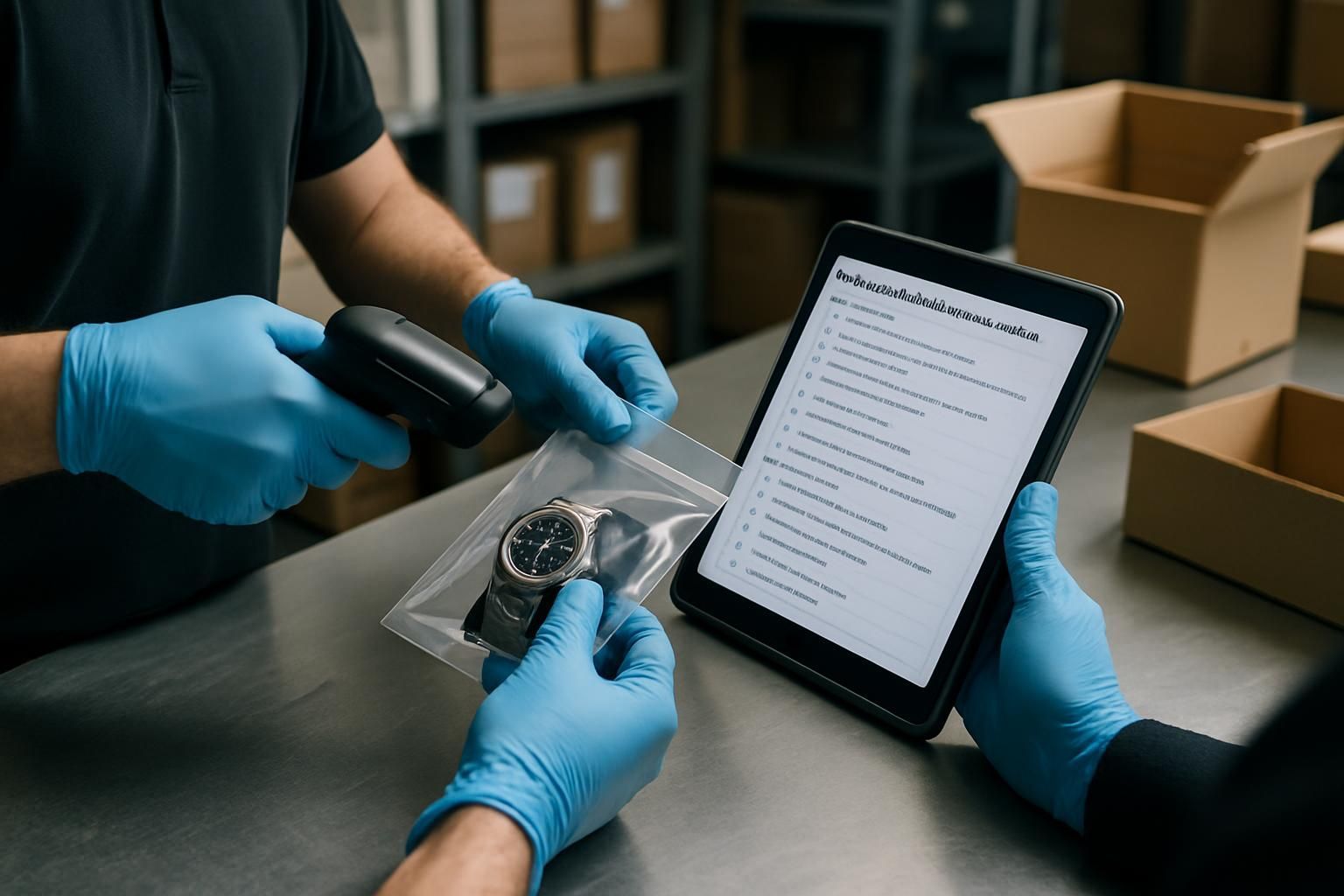
High-value stock is where small process gaps turn into big losses. This high-value stock handling checklist gives operations teams a practical, repeatable way to receive, store, move, count, and dispatch high-risk items with a clear audit trail.
The goal is simple: stop guessing. Start knowing — who handled what, when, where it went, and what to do when something looks off.
What this high-value stock handling checklist covers
Use it to standardise the critical moments where shrink, disputes, and errors tend to happen:
- Preparation checks (access control, secure area, CCTV, tools)
- Receiving and verification (packaging, seals, quantities, serial numbers)
- Storage and movement controls (location logging, chain of custody)
- In-process checks (pick/pack, counts, dispatch handover)
- Escalation criteria (when to pause, isolate, and notify)
- Close-out actions (system updates, evidence capture, sign-off)
When to use it
Run the checklist any time you handle high-value items, including:
- Goods-in deliveries and supplier returns
- Stock transfers between sites, cages, or secure locations
- Cycle counts and investigations
- Customer orders, click and collect, and dispatch
Escalation triggers (do not carry on regardless)
If any of these happen, pause the process, secure the items, preserve evidence, and escalate to the agreed contact:
- Quantity mismatch or missing item
- Serial number mismatch
- Broken or missing tamper seals
- Packaging appears opened, resealed, or damaged
- CCTV is down or coverage is blocked
- Unauthorised access or suspicious behaviour
- Dispatch handover cannot be verified
How to get better results from the checklist
High-value stock handling fails when records are completed later, responsibilities are unclear, or exceptions are treated as “probably fine”. Keep it tight:
- Log location and serials in the moment, not at the end of the shift
- Use dual control for counts and transfers where risk is highest
- Capture photos for any exception, even if it looks minor
- Make handovers explicit: who owns the next action and by when
Run this in Ocasta
Ocasta turns checklist activity into evidence and insight — so you can see where exceptions happen, which steps get missed, and where to tighten controls across sites.
Disclaimer: This checklist is for general guidance only and does not constitute legal, regulatory, health and safety, or professional advice. You are responsible for ensuring compliance with applicable laws, standards, and internal policies.
Included questions
Here's what's included in this high-value stock checklist:
Preparation and access control (6)
Set the conditions for safe, consistent handling before any high-value stock is touched.
-
Yes/No
Are only authorised staff handling high-value stock today?
Confirm access permissions and that no unauthorised colleagues are involved in receiving, moving, counting, or dispatch.
-
Yes/No
Is the two-person rule in place for counts and transfers (where required)?
Use dual control for high-risk steps such as opening secure storage, stock counts, and dispatch handover.
-
Yes/No
Is the secure handling area clear, tidy, and free from customer view?
Remove distractions and keep high-value items out of sight at all times.
-
Yes/No
Is CCTV operational and covering the handling and storage areas?
If CCTV is down or coverage is blocked, pause high-value handling and escalate.
-
Yes/No
Is secure storage locked and access logging in place?
Confirm keys, codes, or access cards are controlled and access can be traced.
-
Yes/No
Are the required tools ready (scanner, labels, tamper seals, paperwork)?
Avoid leaving items unattended while searching for equipment.
Receiving and verification (6)
Stop guessing at the door. Verify what arrived, in what condition, and with what evidence.
-
Yes/No
Do the delivery details match the expected shipment (supplier, date, reference)?
Check the delivery note or manifest against the expected order before opening.
-
Dropdown
What is the condition of the outer packaging?
If damaged, opened, or resealed, photograph and escalate before accepting.
-
Yes/No
Are tamper seals intact (if present)?
Record seal numbers where applicable. If missing or broken, escalate.
-
Yes/No
Have all serial numbers or unique IDs been captured and matched?
Scan or record serials/IMEIs/asset IDs and confirm they match the manifest and system records.
-
Yes/No
Does the quantity received match the delivery paperwork and system expectation?
If there is any discrepancy, do not ‘balance it later’ — isolate and escalate.
-
Yes/No
Have photos been taken for any exceptions (damage, seal issues, discrepancies)?
Photograph labels, seals, and any visible damage for an audit trail.
Storage and movement controls (5)
Keep high-value stock secure and traceable through every movement.
-
Yes/No
Were high-value items never left unattended during handling?
If you must step away, lock items back into secure storage first.
-
Yes/No
Has each item been logged to the correct secure location (bin, cage, safe)?
Update the system immediately to prevent ‘lost in the building’ incidents.
-
Yes/No
Have all access events been recorded (who, when, why)?
Use access logs or the checklist notes to create a clear chain of custody.
-
Yes/No
Are all transfers authorised and referenced (job number, ticket, request)?
No ad-hoc moves. Every movement needs a reason and a record.
-
Yes/No
Is chain of custody confirmed for each handover?
Both parties confirm item identity and condition at the point of handover.
In-process checks during picks, counts, and dispatch (5)
Reduce shrink and rework by checking the right things at the moment risk is highest.
-
Yes/No
Were picks completed against the system (not memory or paper-only)?
Scan items where possible to prevent selection errors.
-
Yes/No
Were serial numbers or unique IDs rechecked at pick/pack?
Confirm the right item, not just the right product name.
-
Percentage
What is the stock count variance for high-value items (if a count was completed)?
Enter the variance percentage for the count session. If variance is above tolerance, escalate immediately.
-
Yes/No
Were correct packaging and tamper controls applied for dispatch?
Use approved packaging, seals, and labels. Record seal numbers if required.
-
Yes/No
Was dispatch handover verified (identity, reference, and item match)?
Confirm courier/driver identity and match items to dispatch references before release.
Escalation criteria and incident handling (5)
Know when to stop and escalate — before a small issue becomes a loss.
-
Yes/No
Were any discrepancies isolated and secured immediately?
Do not continue processing. Isolate the items, secure the area, and preserve evidence.
-
Dropdown
Did any escalation triggers occur?
Select the most relevant trigger. If any trigger occurs, notify the right person and log the incident.
-
Person
Who was notified?
Choose the manager, loss prevention lead, or operations contact you escalated to.
-
Text
Incident or ticket reference
Add the reference number (if raised) so the audit trail is complete.
-
Text
What happened and what actions were taken?
Keep it factual: what you saw, what you checked, what you secured, and next steps agreed.
Close-out and audit trail (5)
Finish the job properly so the next person is not forced to guess.
-
Yes/No
Have all system updates been completed (received, moved, picked, dispatched)?
No end-of-shift catch-up. Update in the moment to keep records trustworthy.
-
Yes/No
Is secure storage relocked and keys/codes controlled?
Confirm keys are returned to the correct place and access is not shared.
-
Yes/No
Are required documents captured and stored (delivery note, manifest, photos, seal records)?
Attach evidence to the relevant record so it is easy to find later.
-
Yes/No
Has a handover been completed for any open issues?
If anything is unresolved, name the owner and the next check time.
-
Signature
Sign off
By signing, you confirm the checks were completed and exceptions were escalated.